Table of Contents
ToggleA Smarter Way to Control Keys and Protect Commercial Property
Physical keys are still the most common access method in small businesses.
They are also one of the least controlled.
Industry reports consistently show that a significant percentage of break-ins involve no forced entry. In many cases, access is gained using copied or unreturned keys.
Former employees, contractors, and short-term tenants often retain keys. Standard key systems cannot prevent unauthorized duplication. Once a copy exists, you lose visibility and control.
A restricted key system solves this problem by placing duplication control and authorization back in the hands of the business owner.

What Is a Restricted Key System
A restricted key system is a patented key control solution designed to prevent unauthorized duplication and improve access accountability.
Only authorized locksmiths can produce duplicate keys. Written approval from the owner is required before any copy is cut.
Each key is uniquely identified and recorded. This creates a traceable chain of custody for every credential in circulation.
Core Components
- Patent-protected keyway design
- Controlled key blank distribution
- Unique key numbering
- Master key hierarchy options
- Authorized duplication process
This structure turns ordinary mechanical keys into managed access credentials.
Why Traditional Keys Create Hidden Risk
Standard keys can be duplicated at hardware stores without verification.
This creates three problems for businesses:
- Unknown copies in circulation
- No audit trail
- Costly lock replacement when keys are lost
A retail store with frequent staff turnover can accumulate uncontrolled duplicates within months. A small warehouse may need to rekey multiple doors after one missing key.
Restricted systems remove duplication risk at the source.
The Business Advantages of a Restricted Key System
1. Controlled Key Duplication
Only designated locksmiths can cut new keys.
Each request requires documented authorization. Unauthorized copies cannot be made legally because key blanks are protected.
Business impact
You eliminate silent duplication and regain full control over physical credentials.
2. Full Key Tracking and Accountability
Every issued key is logged with:
- Holder name
- Issue date
- Access level
- System number
If an employee leaves, you know exactly which areas were accessible.
Business impact
You reduce liability and simplify internal audits.
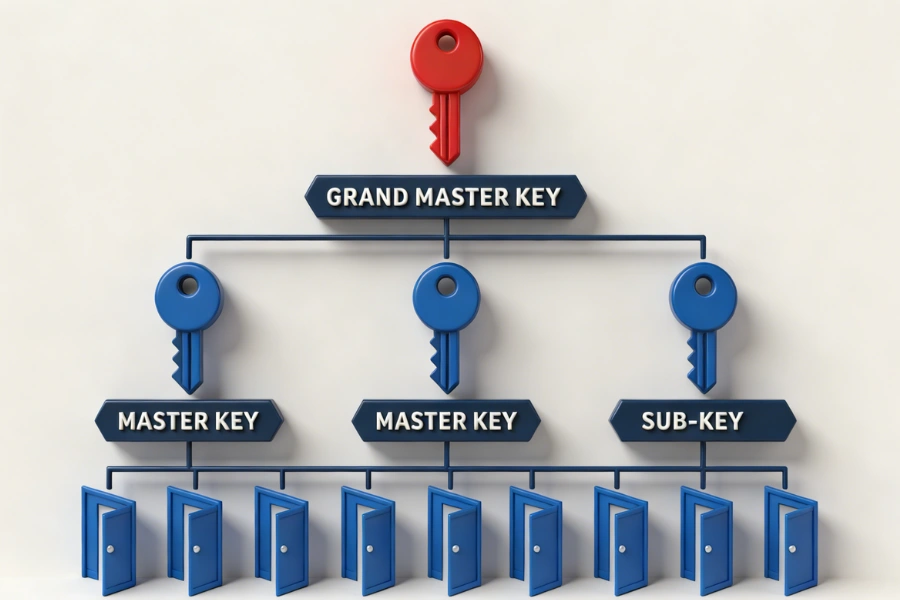
3. Master Key Structure with Tiered Permissions
Restricted systems support scalable master key hierarchies.
For example:
- Store manager opens all areas
- Staff access only assigned rooms
- Cleaning crew opens after-hours entry points only
Business impact
You match access to job roles without overexposing sensitive areas.
4. Higher Physical Security
High-security cylinders in restricted systems often include:
- Anti-pick features
- Anti-bump protection
- Drill-resistant components
- Complex key geometry
Business impact
You reduce vulnerability to manipulation and forced attacks while maintaining mechanical reliability.
5. Lower Long-Term Operating Costs
When a standard key is lost, many businesses replace entire lock sets.
With a restricted system, you can:
- Cancel a key
- Replace a single cylinder if required
- Maintain the rest of the system intact
Business impact
You avoid repeated rekeying expenses as your business grows.
6. Scalable Expansion
As your business expands to new offices, storage rooms, or locations, additional cylinders can be integrated into the same system.
There is no need to replace existing hardware.
Business impact
Your access structure grows with your operations.
Where Restricted Key Systems Work Best
Restricted key systems are especially effective in environments with multiple users and turnover.
Common applications include:
- Retail stores
- Office suites
- Medical clinics
- Educational facilities
- Apartment complexes
- Warehouses
- Light industrial facilities
- Government buildings
Small and mid-sized businesses benefit most because they often lack dedicated security teams but still need strong access control.
How to Evaluate a Restricted Key System Before Installation
Choosing the right platform requires careful review.
Patent Protection
- Confirm patent validity
- Check expiration timeline
- Ensure enforcement in your region
Once a patent expires, duplication protection weakens.
Authorized Distribution Network
- How many locksmiths can service the system
- Is duplication tightly controlled
- Is there a clear approval process
Too many distributors reduce control. Too few may affect service speed.
Contract Terms
- Owner retains duplication authority
- Clear key request workflow
- Defined responsibility for records
The business owner should always control key authorization.
Record Management
A secure system requires documentation.
Options include:
- Digital tracking logs
- Centralized key databases
- Controlled sign-out procedures
This converts keys into managed credentials rather than unmanaged metal copies.
Lock Type Selection
Select hardware based on:
- Door material
- Usage frequency
- Required security grade
Common options include:
- Euro profile cylinders
- Oval cylinders
- Modular cylinders
- Padlocks
- High-security cylinders
For businesses considering future upgrades, mechanical systems can integrate with smart cylinders that support mobile credentials and remote management.
Mechanical and Smart Integration Options
Modern businesses often combine mechanical control with electronic oversight.
Smart cylinder options may include:
- App-based management
- Fingerprint authentication
- Time-based permissions
- Remote credential updates
This hybrid model preserves mechanical reliability while introducing scalable access management.
For example, a small co-working space can issue temporary mobile access while maintaining restricted mechanical backups for core entry points.
Maintenance and Lifecycle Planning
Restricted key systems require minimal maintenance but should be reviewed periodically.
Best practices include:
- Annual hardware inspection
- Key record audits
- Patent expiration review
- Access structure updates during staff changes
When employees leave, collect keys immediately and update records.
If a high-risk key is lost, replace only the affected cylinder rather than the entire system.
Why Hardware Precision Matters in Restricted Systems
Duplication control depends on precision manufacturing.
Cylinder tolerances, keyway accuracy, and material quality directly affect:
- Pick resistance
- Key stability
- Long-term durability
- Master key hierarchy integrity
A poorly manufactured cylinder weakens even the best duplication control strategy.
EOS SECURE delivers precision-engineered mechanical and electronic lock cylinders backed by more than a decade of manufacturing expertise. Established in 2011, our factory operates under ISO9001 and ISO14001 certifications, ensuring every product meets rigorous international standards including EN1303 and SKG. With over 50 advanced Swiss-type CNC automatic lathes and integrated machining centers, we manufacture high-quality lock cylinders trusted by clients across industries worldwide. Whether you need small-batch customization or large-scale production, EOS SECURE provides reliable performance, consistent quality, and dependable technical support.
Final Thoughts
A restricted key system transforms traditional keys into controlled business assets.
You gain:
- Duplication control
- Clear accountability
- Scalable access hierarchy
- Reduced long-term costs
- Improved physical security
For small businesses and property managers, it offers structured access without the complexity of full electronic systems.
Explore EOS SECURE solutions to strengthen your business security with scalable, precision-engineered access control.
FAQ
What is a restricted key system?
A restricted key system is a patented access solution that prevents unauthorized key duplication. Only approved locksmiths can cut copies with written authorization, giving businesses full control over who holds active credentials.
How much does a restricted key system cost?
Initial costs are higher than standard locks. However, long-term savings often result from reduced rekeying, improved access control, and lower risk exposure when keys are lost or staff turnover occurs.
Can a restricted lock be picked?
High-security restricted cylinders include anti-pick and anti-bump features. While no mechanical lock is invulnerable, these systems significantly reduce manipulation risks compared to standard commercial locks.
Are restricted keys impossible to duplicate?
They cannot be legally duplicated outside authorized channels. Patent-protected key blanks and controlled distribution prevent hardware stores or unauthorized locksmiths from producing valid copies.
Is a master key system included?
Yes. Most restricted systems support tiered master key structures, allowing business owners to assign different access levels while maintaining centralized control over the entire property.