Keys appear simple, yet the small grooves along a key blade determine whether a lock opens or stays secure. These grooves are known as key bitting.
Key bitting defines the depth and spacing of cuts on a key. These cuts interact with the internal pins of a lock cylinder, allowing the mechanism to rotate only when the correct key is inserted.
For businesses that rely on physical locks, understanding key bitting helps explain how key systems function, how master keys work, and how access control can be managed across multiple doors.
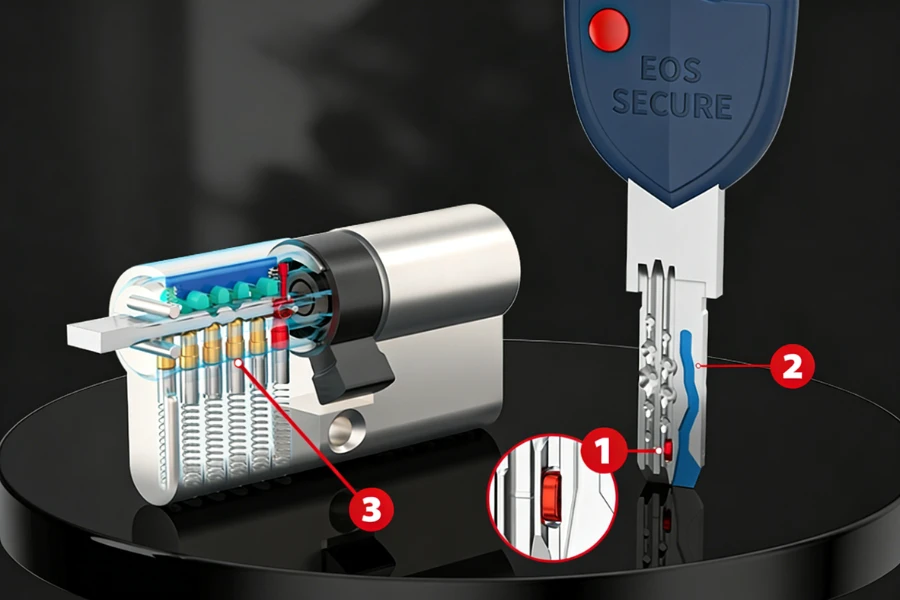
Table of Contents
ToggleWhat Is Key Bitting
Key bitting refers to the pattern of grooves cut along the blade of a key. Each groove has a specific depth that corresponds to the internal pin structure of a lock cylinder.
When the correct key is inserted, these cuts lift the lock pins to precise heights. Once all pins align at the shear line, the cylinder rotates and the door unlocks.
In commercial environments, this precise alignment allows businesses to control which keys open specific doors.
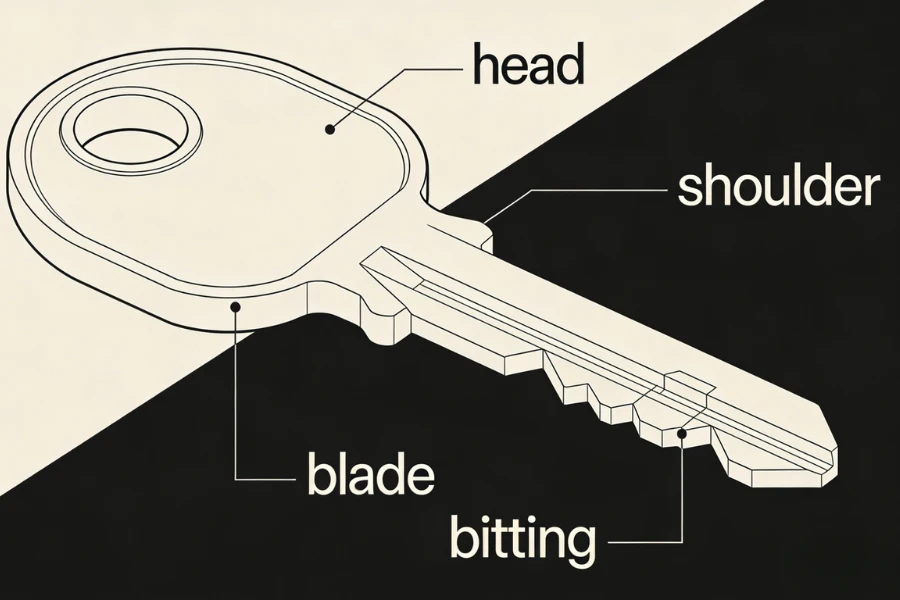
Key Anatomy – Where Key Bitting Is Located
A standard mechanical key includes several parts that work together with the lock cylinder.
These components include
Head – the portion held by the user
Shoulder – the point that stops the key from inserting too far
Blade – the working section inserted into the cylinder
Bitting – the series of grooves along the blade
The bitting is the functional portion of the key. Its depth pattern determines how the internal pins inside the cylinder will align.
How Key Bitting Works Inside a Lock
Most commercial door locks use a pin tumbler mechanism. This system relies on a series of pins that must align precisely before the cylinder can rotate.
When a key enters the cylinder, its bitting lifts each pin to a specific height. If all pin pairs align with the shear line, the cylinder plug can turn.
If the cuts are incorrect, the pins block rotation and the lock remains secure.
Pin Tumbler Components
A typical pin tumbler cylinder contains
Key pins
Driver pins
Springs
Cylinder plug
Each component works together to ensure that only a correctly cut key can align the pins and operate the lock.
The Shear Line
The shear line is the boundary between the cylinder plug and the outer housing. When all pins align at this point, the plug can rotate freely.
Even small variations in key bitting can prevent alignment, which is why accurate key cutting is essential for reliable lock performance.
How Key Bitting Codes Work
Lock manufacturers often represent bitting patterns using numerical codes. Each number corresponds to a specific cut depth on the key.
For example, a sequence such as
3 2 5 1 4
represents the order of cut depths along the key blade.
Locksmiths and manufacturers use these codes to reproduce keys or configure lock systems without requiring the original key.
Bitting charts define the exact depth associated with each number.
How Key Bitting Affects Lock Security
The design of bitting patterns directly influences the security of a key system.
Simple or predictable patterns can reduce the number of available combinations. More complex patterns increase the difficulty of unauthorized duplication or manipulation.
For businesses managing multiple doors, well-designed bitting structures help maintain reliable access control.
Weak Bitting Structures
Some bitting patterns reduce system security
Repeated shallow cuts
Limited variation between depths
Predictable sequences
These patterns may reduce the number of unique key combinations available.
Strong Bitting Structures
Secure key systems typically use
Greater variation in cut depths
Balanced spacing between cuts
Controlled duplication policies
These factors increase the number of possible key combinations within a system.
High Security Cylinder Designs
Modern high-security cylinders may include additional protection features
Sidebars
Secondary pin systems
Restricted key profiles
These features work alongside complex bitting patterns to increase resistance to unauthorized duplication.
How Key Bitting Supports Master Key Systems
Key bitting is essential for master key systems commonly used in offices, retail spaces, and apartment buildings.
A master key system allows different keys to open different doors while still enabling a master key to open multiple locks.
This is achieved through specially designed bitting structures that create multiple possible pin alignments within a cylinder.
For example
An employee key opens a specific office
A supervisor key opens several rooms
A master key opens the entire facility
This structured approach helps businesses manage access while reducing the number of physical keys required.
Common Key Bitting Problems
Incorrect or worn bitting patterns can cause operational issues in lock systems.
Understanding these problems helps businesses maintain reliable security.
Why Key Copies Sometimes Fail
If a duplicate key is cut slightly incorrectly, it may not raise the pins to the correct height.
This can lead to
Difficulty turning the lock
Incomplete pin alignment
Intermittent operation
Accurate key duplication is essential for stable lock performance.
Rekeying vs Replacing Locks
When keys are lost or employee access needs change, rekeying is often more efficient than replacing the entire lock.
Rekeying changes the internal pin configuration and creates a new bitting pattern while keeping the same lock hardware.
This approach helps businesses maintain security while reducing replacement costs.
How Businesses Choose Secure Key Systems
Selecting a reliable lock system involves more than choosing a cylinder type.
Businesses should evaluate
Key duplication control
Master key compatibility
Long-term durability
Scalability for future expansion
A well-designed key system allows companies to manage access levels while maintaining consistent security across multiple doors.
Maintenance Tips for Keys and Lock Cylinders
Mechanical lock systems require routine maintenance to ensure long-term reliability.
Practical maintenance practices include
Keeping keys clean and undamaged
Avoiding excessive force when turning locks
Lubricating cylinders periodically
Replacing worn keys before they affect pin alignment
Routine inspections help prevent operational issues and extend the lifespan of lock hardware.
Strengthening Business Security with Reliable Lock Cylinders
Reliable key systems depend on precision manufacturing and consistent cylinder performance.
EOS SECURE delivers precision-engineered mechanical and electronic lock cylinders backed by more than a decade of manufacturing expertise. Established in 2011, our factory operates under ISO9001 and ISO14001 certifications, ensuring every product meets rigorous international standards including EN1303 and SKG.
With more than 50 advanced Swiss-type CNC automatic lathes and integrated machining centers, EOS SECURE produces high-quality lock cylinders trusted by businesses, security integrators, and distributors worldwide.
Whether you require customized key systems or large-scale cylinder production, EOS SECURE provides reliable performance, consistent quality, and dependable technical support.
Explore EOS SECURE solutions to strengthen your business security.
FAQ
What is key bitting in a lock?
Key bitting is the pattern of grooves cut along a key blade. Each groove has a specific depth that lifts the pins inside a lock cylinder to the correct height, allowing the pins to align at the shear line so the lock can rotate.
How to identify key bitting?
Key bitting can be identified by examining the series of grooves along the key blade. Locksmiths often measure the depth of each cut or use a bitting code chart provided by the lock manufacturer to determine the exact pattern.
What is a key bitting chart?
A key bitting chart is a reference table used by locksmiths and manufacturers. It shows the relationship between numerical bitting codes and the actual depth measurements used when cutting keys for a specific lock system.
Can two keys have the same bitting?
Yes. Two keys can share the same bitting pattern if they are designed for the same lock system. However, high-security locks often use restricted key profiles and controlled duplication to prevent unauthorized copying.
