Many small businesses believe that upgrading to a higher-rated cylinder automatically improves security.
But in practice, lost keys and uncontrolled duplication cause more real-world breaches than forced entry.
The overlooked factor behind this problem is the key profile.
If your key profile is open and unrestricted, anyone can duplicate your keys.
If it is protected and controlled, you decide who can create copies.
That difference directly affects long-term business security.
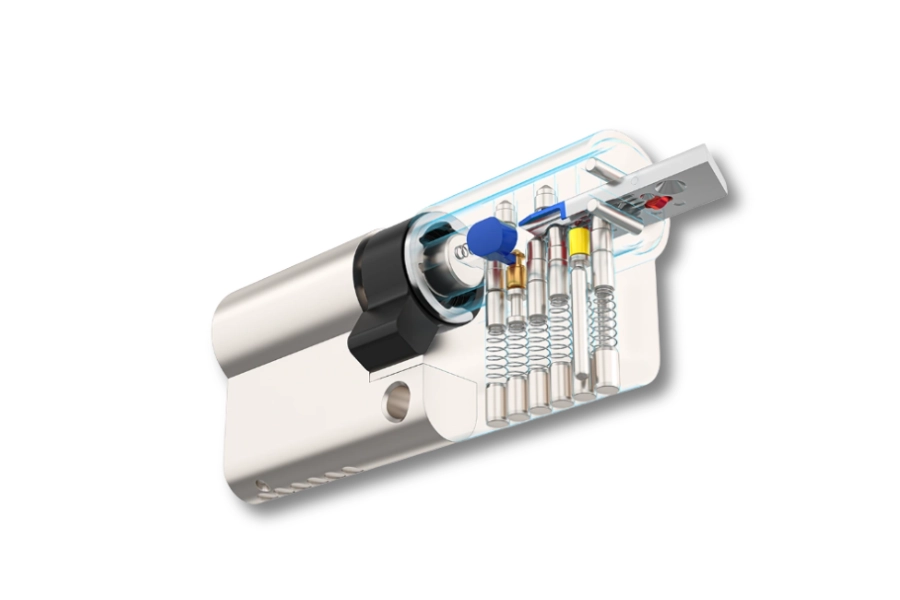
Table of Contents
ToggleWhat a Key Profile Is and Why It Matters
A key profile refers to the cross-sectional shape of the key blade and the matching keyway inside the cylinder.
It determines:
- Whether a key can enter a lock
- Whether blank keys are freely available
- Whether duplication requires authorization
- Whether your locking system can scale securely
Many businesses focus on cylinder shape or brand name.
However, the key profile determines who controls access in the long run.
The cylinder protects the door. The key profile protects the system.
The Real Business Risk – Uncontrolled Key Duplication
Consider a small retail shop with five employees.
If one staff member leaves and had copied their key, you have no way of knowing how many duplicates exist.
Replacing the entire locking system becomes the only reliable solution.
An open key profile makes duplication easy and invisible.
A patented key profile changes the equation:
- Duplication requires authorization
- Key blanks are restricted
- Copies are traceable
- Former employees cannot reproduce keys independently
For businesses with staff turnover, contractors, or shared access, this is not a technical detail.
It is operational risk management.
Cylinder Profile vs Key Profile – Why Compatibility Is Not Enough
Cylinder profile refers to the outer shape of the cylinder body, such as:
- Euro profile
- Oval profile
- Rim cylinder
- Mortise cylinder
- SFIC or LFIC interchangeable cores
This determines whether the lock fits your door.
Key profile determines whether your access control remains secure over time.
A business can install a high-security Euro cylinder and still face exposure if the key profile is open and widely available.
Compatibility solves installation.
Profile control solves duplication risk.
Open vs Patented Key Profiles – A Cost and Risk Comparison
Open Key Profiles
Open profiles are inexpensive and widely available.
Short-term advantage:
- Lower upfront cost
- Easy duplication
Long-term risk:
- No duplication control
- High exposure when staff leave
- Rekeying entire premises after lost keys
- No structured expansion path
An open profile may seem economical.
But frequent rekeying and security uncertainty increase long-term cost.
Patented Key Profiles
Patented profiles restrict blank distribution and require authorization for duplication.
Business advantages:
- Controlled access lifecycle
- Reduced rekey frequency
- Clear accountability
- Structured master key expansion
For growing businesses, the difference becomes measurable over time.
The cost of uncontrolled duplication often exceeds the cost of a protected key profile.
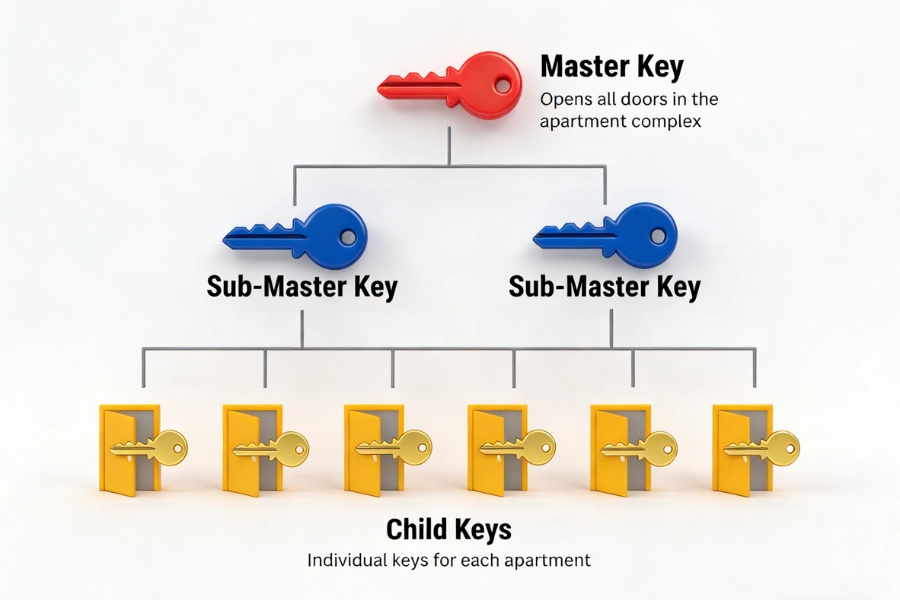
How Key Profiles Affect Master Key Systems
A master key system allows layered access:
- Individual room keys
- Department-level access
- One master key for management
If the key profile is open, any copied key can compromise the hierarchy.
If the profile is protected:
- Expansion remains secure
- New doors integrate smoothly
- Old keys can be phased out systematically
- Control remains centralized
Without profile control, master key planning loses integrity.
Staff Turnover and Rekeying – A Practical Example
Imagine a small office with 12 employees.
Two employees leave per year.
Keys are not tracked. Copies may exist.
With an open profile:
- You must replace cylinders or accept ongoing risk.
With a protected profile:
- You know duplication requires authorization.
- Risk remains contained.
In environments with higher turnover, interchangeable core systems such as SFIC can reduce downtime.
But duplication control still depends on the key profile.
Operational efficiency and profile protection must work together.
Security Certifications Are Not the Full Picture
Standards such as EN1303, SKG, or TS007 measure resistance against:
- Drilling
- Picking
- Snapping
- Pulling
These certifications are important.
However, they do not address uncontrolled key duplication.
A cylinder may resist physical attack but still allow unlimited key copies if the profile is open.
True business security combines:
- Physical resistance
- Controlled key profile
- Clear access policy
- Long-term system planning
Security is not only about breaking the lock.
It is also about controlling who can recreate the key.
Smart Locks and Mechanical Backup – A Common Oversight
Many electronic cylinders retain a mechanical override keyway.
If that backup uses an open profile, the entire smart system can be undermined.
A secure strategy ensures:
- Mechanical override keys use protected profiles
- Duplication remains controlled
- Access rules apply consistently
Hybrid systems require consistent security thinking across mechanical and electronic components.
When It Is Time to Review Your Key Profile Strategy
You should reassess your key profile if:
- Employees leave regularly
- Contractors access your premises
- Keys have been copied without tracking
- You are expanding into multiple locations
- You plan to implement a master key structure
Upgrading the key profile is often less disruptive than replacing entire lock hardware.
It strengthens control without interrupting operations.
How to Choose the Right Key Profile for Your Business
For small retail stores:
- Protected profile recommended
- Simple hierarchy
- Limited authorized duplication
For offices with staff rotation:
- Patented profile
- Master key planning
- Clear duplication authorization process
For property managers:
- Interchangeable core format
- Protected key section
- Scalable structure
For multi-site businesses:
- Unified key profile standard
- Centralized control
- Long-term expansion compatibility
The correct profile reduces uncertainty and supports growth.
Final Takeaway – Control Determines Security
A key profile is not just a mechanical shape.
It defines who controls duplication, how your system scales, and whether your security remains stable over time.
Small businesses often invest in visible hardware upgrades.
But sustainable security comes from controlled access management.
Choose a key profile that protects not only today’s door, but tomorrow’s expansion.
EOS SECURE designs and manufactures mechanical and electronic lock cylinders with a strong focus on key profile control and system scalability. Since 2011, we have supported distributors, property managers, and commercial projects with protected key sections, master key planning, and customizable cylinder formats including Euro, Oval, Rim, SFIC, and LFIC configurations. Operating under ISO9001 and ISO14001 certifications and meeting standards such as EN1303 and SKG, EOS SECURE helps businesses implement locking systems built for long-term control rather than short-term replacement. Explore EOS SECURE solutions to strengthen your business security with structured, scalable access management.
FAQ
What is a key profile?
A key profile refers to the cross-sectional shape of a key blade and the matching keyway inside a cylinder. It determines whether a key can enter the lock and whether duplication can be controlled through patented or restricted key sections.
Is a key profile the same as a cylinder profile?
No. A cylinder profile defines the external shape of the lock body, such as Euro or Oval. A key profile defines the internal keyway design that controls key compatibility and duplication security.
Are patented key profiles worth the extra cost?
For businesses with staff turnover or shared access, patented key profiles reduce unauthorized duplication and long-term rekeying costs. They provide structured control that often outweighs the higher initial investment.
Can an open key profile be upgraded to a protected one?
Yes. In many cases, the cylinder can be replaced without changing the entire door hardware. Upgrading to a protected key profile improves duplication control while maintaining door compatibility.